Money laundering is a sophisticated, multi-step process involving the placement, layering and integration of illicit funds. It poses a serious threat to financial institutions and the wider economy. Without an effective anti-money laundering and counter-terrorism financing (AML/CFT) compliance program and AML investigation tools within the institution, criminals would be free to launder their money without restriction or further consequence.
Effective internal investigation of unusual customer behavior or transaction patterns that lack economic logic is one of the key pillars of AML/CFT compliance programs.
Put simply, internal ML/TF investigations are the systematic analysis of unusual activities to determine whether these activities give rise to suspicion that a customer is engaged in money laundering, terrorist financing or other criminal activity.
While not all unusual activity will give rise to suspicion of money laundering, an abundance of caution is required to ensure regulatory compliance. And this is where a thorough internal investigation is of paramount importance – for a regulated institution to formulate reasonable grounds for suspicion that its customer is engaged in, or attempting to engage in, money laundering or terrorist financing.
Non-negotiable necessity
The AML/CFT legislation sets out strict guidelines for obliged entities to report to the Financial Intelligence Unit (FIU) any customer activity where the obliged entity knows, suspects or has reasonable grounds to suspect that funds, regardless of the amount, are the proceeds of criminal activity or related to terrorist financing.
On the one hand, non-compliance, even inadvertent, can have serious consequences, including heavy fines and loss of customer confidence. On the other hand, reporting unusual customer behavior to the FIUs without reasonable grounds for suspecting money laundering or other criminal activity could result in the authorities being overburdened with defensive reporting.
Having a robust internal ML/TF investigation process is therefore not a choice, but an absolute necessity. In practice, we have seen a number of regulatory sanctions stem from deficiencies in internal ML/TF investigations. Even when a transaction is flagged as unusual by the monitoring system, the failure to follow up on the alert leads to a failure to report the customer to the FIU.
Triggers for internal AML investigation
A transaction that appears unusual is not necessarily suspicious. Customers with a stable and predictable transaction profile will sometimes have transactions that are unusual for them or, for perfectly legitimate reasons, have an erratic pattern of transactions or account activity. The unusual behavior is merely a basis for further ML/TF investigation, which may or may not lead to a judgement as to whether it is suspicious.
Thus, the request for an internal ML/TF investigation is triggered by the unusual activity of the customer. The unusual activity could be triggered by:
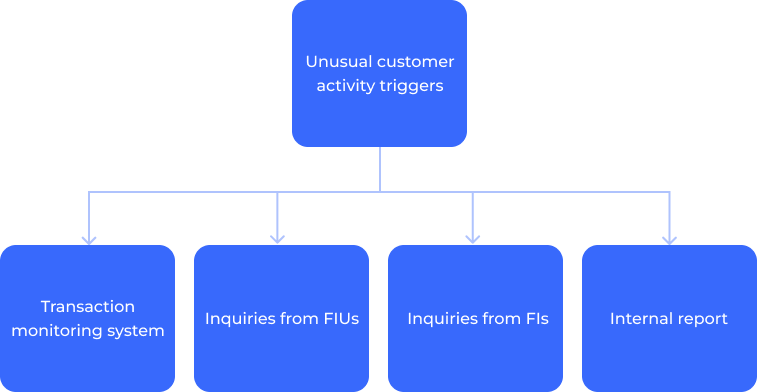
- Transaction monitoring system.Unusual or uncharacteristic behavior by a customer is often defined by the rules of the automated transaction monitoring system. It is important that the rules and scenarios of the automated transaction monitoring system have an appropriate definition of the ‘unusual nature of a transaction’, e.g., unusual size or frequency of transactions for that customer or peer group; unusual nature of transactions; unusual geographical destination or origin of a payment or payments to or from a high-risk country, etc. It is important that the rules of the automated transaction monitoring system take into account all known ML/TF threats and typologies. It is important that transaction monitoring rules take into account all known ML/TF threats or typologies.
- Inquiries from the FIUs, law enforcement authorities or supervisory bodies.Inquiries by the FIUs, law enforcement or regulatory authorities are not typical of a routine business relationship with a customer. While the inquiry itself may not necessarily indicate suspicion, the fact that such authorities are making inquiries is unusual in the ordinary course of business and may be the basis for further ML/TF investigation.
- Inquiries from the correspondent financial institutions (FIs).Unusual activity can be also triggered by inquiries from the correspondent financial institutions on the customer transactional behavior. It is possible that atypical transactional patterns are prompted by the counterparty financial institution, leading them to seek additional details on the transaction. The recurrent nature of these inquiries may serve as an indication for further ML/TF investigation.
- The internal report on unusual activities.It is essential to recognize the importance of the vigilance of staff and their ability to report unusual customer behavior within the institution through the use of the internal unusual activity report. Factors such as staff intuition, direct contact with a customer, the ability through practical experience to recognize transactions that do not seem to make economic sense for that customer should be taken into account and the in-depth internal ML/TF investigation should be initiated.
If unusual activity cannot be rationally explained, it may involve money laundering, terrorist financing or other criminal activity. However, a suspicion without evidence is merely a subjective opinion. To move beyond speculation, the firm must have a reasonable basis for suspicion, supported by documentary evidence or the lack of it (such as a customer’s failure to provide reasonable information about the unusual transaction).
A step-by-step breakdown of AML investigation
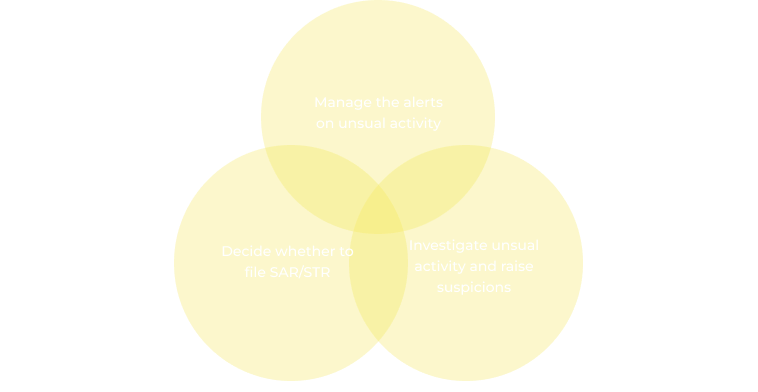
In general, an effective internal AML investigation process includes these basic components:
- manage the alerts on unusual activity;
- investigate unusual activity and raise suspicions;
- deciding whether to file a suspicious transaction (activity) report (confirming or rejecting the suspicion).
Basic components for an effective ML/TF internal investigation process
Step one: alert management
The journey begins when a red flag is raised, typically within the institution’s transaction monitoring system. Launching a full investigation on every alert of unusual activity can be resource intensive. Therefore, the first step is to determine whether an investigation is warranted. Alert management focuses on the processes used to evaluate identified unusual activity alerts, close the false positives, and decide on the priorities for further investigation of the true positives.
A preliminary manual review of the flagged account or activity can help assess the need for further investigation and close false positive alerts. A developed risk scoring system for transaction monitoring alerts that assigns higher scores to transactions that have characteristics associated with higher risk can help prioritize alerts and focus on those that are inherently higher risk.
Step two: investigate unusual activity and raise suspicions
Investigating transactions or suspicious customer behavior is one step towards establishing reasonable suspicion. Transactions that have no apparent economic or legitimate purpose may be more likely to be involved in money laundering or terrorist financing activities.
Analyzing the economic logic of a transaction involves assessing whether the transaction makes sense in the context of the parties involved, their usual business activities and broader economic considerations. In assessing the existing business relationship between the parties to the transaction, it is necessary to identify and understand not only the source of funds used for the transaction, but also the stated purpose of the transaction. It is also important to consider industry standards and norms to determine whether the transaction is consistent with customary practices in the relevant industry.
Verification of the legitimate purpose of the transaction requires documentary evidence. If the pattern of transactions and the information previously provided by the customer raise concerns that the transaction or the customer’s overall behavior is related to possible criminal activity or lacks economic logic, it is of paramount importance to verify the existence of proper documentation and supporting evidence for the transaction in relation to the stated purpose of the transaction and the source of funds. Lack of documentation or unclear records may raise suspicion.
Step three: decide whether to file Suspicious transaction (activity) report
Institutions are not required to investigate or confirm the underlying criminal activity (e.g,
terrorist financing, money laundering, tax evasion, various types of fraud, etc.). These types of investigations are the responsibility of law enforcement agencies. However, when assessing unusual activity, institutions should, to the best of their ability, identify the characteristics of the suspicious activity in order to confirm or reject the suspicion initially raised by the reported unusual transaction or customer behavior.
The decision as to whether there are sufficient grounds for suspicion to be reported to the FIU must be made by the Money Laundering Reporting Officer. After reviewing the triggers, analyzing the results of the ML/TF investigation, and considering all relevant information, the ML/TF Officer must decide whether the reported activity warrants the filing of a Suspicious Transaction Report (SAR/STR). A comprehensive analysis is the basis of the SAR/STR. The report should not be a mere compilation of facts, but a well-reasoned document that justifies the need for further action. You can read what the STR should contain in the Financial Action Task Force (FATF) Recommendation 20.
Challenges in AML investigation
The field of AML investigations is full of challenges. These challenges include:
- Increased regulatory oversight
While AML/CFT regulations have maintained the same basic principle over the decades – the analysis and reporting of suspicious transactions or activities – the requirements for implementing this principle continue to evolve. Overall, there is a growing regulatory emphasis on the quality of internal investigations related to ML/TF. Keeping up with the wave of increased requirements is a daunting task for AML professionals. Based on our observations, regulators are exercising heightened scrutiny, particularly when unusual activities are inadequately investigated, either due to lack of competence or possible “wilful blindness”.
- Adapting to smarter criminals
Money launderers are becoming increasingly sophisticated. AML professionals need to stay one step ahead of these cunning criminals by equipping themselves with the right tools and knowledge. While the various automated tools can help identify unusual activity and manage the ML/TF investigation case (including alert management and case escalation to different levels of authority within and outside the institution), it is the skills of the ML/TF investigator that define the quality of the investigation and the follow-up to STR/SAR.
It is the responsibility of the institution’s management to relieve the ML/TF investigators of manual tasks and to allow them to focus their time on raising awareness of new ML/TF typologies and conducting in-depth research. This automation of the tasks of identifying unusual activities, managing alerts and prioritizing cases allows investigators to devote more time to thorough investigations.
- Alert management
Separating real threats from false positives is a constant challenge. Inefficient monitoring processes can result in a high number of false positives, leading to unnecessary investigations and inflated compliance costs, while inefficient alert management (prioritization) can lead to a lack of a risk-based approach and failure to address high risk cases in a timely manner.
Efficient workflows are essential to manage the volume of cases. Investigations require meticulous attention to detail, including analyzing vast amounts of data, reviewing numerous documents and meeting strict deadlines.
Practices for conducting effective AML investigations
To overcome these challenges and conduct efficient AML investigations, consider the following best practices.
Best practises for effective ML/TF investigations
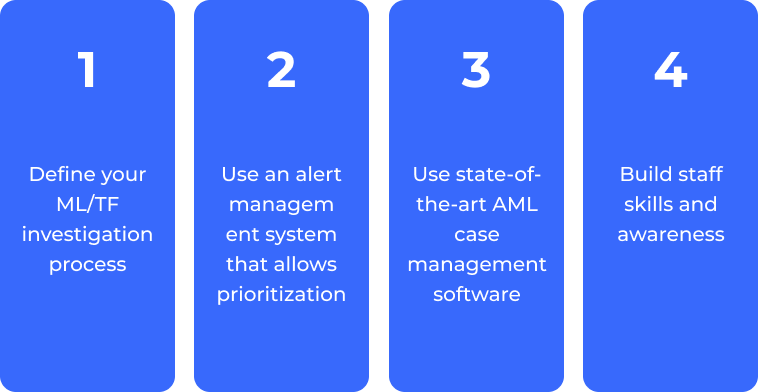
Best Practice 1: Define your AML investigation process
A well-defined ML/TF investigation process ensures consistency, efficiency and scalability. By understanding the specific threats your organization faces, you can tailor your investigation processes accordingly.
Best Practice 2: Use an alert management system that allows prioritization
A developed risk scoring system for transaction monitoring alerts that assigns higher scores to transactions that have characteristics associated with higher risk could help to prioritize alerts and focus on those that inherently present a higher risk of suspicious activity.
Best Practice 3: Use state-of-the-art AML case management software
The volume of data and documentation involved in AML investigations requires advanced case management software. But not all software solutions are created equal. Look for an easy-to-use, flexible system that can streamline the investigation process, from alert generation to report filing. This will reduce the administrative burden and allow your team to focus on analysis.
Best practice 4: Build staff skills and awareness
It is the competence of the ML/TF investigator that determines the quality of the investigation and, consequently, the quality of the STR/SAR once the suspicion of possible criminal activity has been confirmed. Increasing the competence of staff is not only a matter of continuous training programs. Relieving ML/TF investigators of manual tasks could allow them to focus their time on raising awareness of new ML/TF typologies and conducting in-depth research. By automating the tasks of identifying unusual activities, managing alerts and prioritizing cases, investigators will be able to devote more time to thorough investigations.
Strengthening your AML defenses the right way
Financial institutions are at the forefront of the fight against money laundering. Compliance is not optional, it is mandatory. Failure to comply can result in severe penalties and loss of reputation.
An effective AML program, supported by efficient ML/TF investigations, is not just a regulatory requirement; it is good business practice. There are costs associated with running an AML compliance program. An efficient alert management system can help prioritize alerts for further ML/TF investigation, while convenient case management, escalation systems, can save time resources needed for a smooth process flow. Modernizing your case management is more important than ever. AMLYZE provides a highly flexible alert management, case management and escalation system.
With AMLYZE, you can streamline your ML/TF investigation process, stay compliant with changing regulations, and protect your organization from the financial and reputational risks associated with money laundering. Stay ahead of the money laundering threat with AMLYZE’s comprehensive solutions.
With these best practices and the right tools, you can effectively combat money laundering and ensure a secure financial system. Trust AMLYZE to simplify your AML investigations and strengthen your defenses against financial criminals.